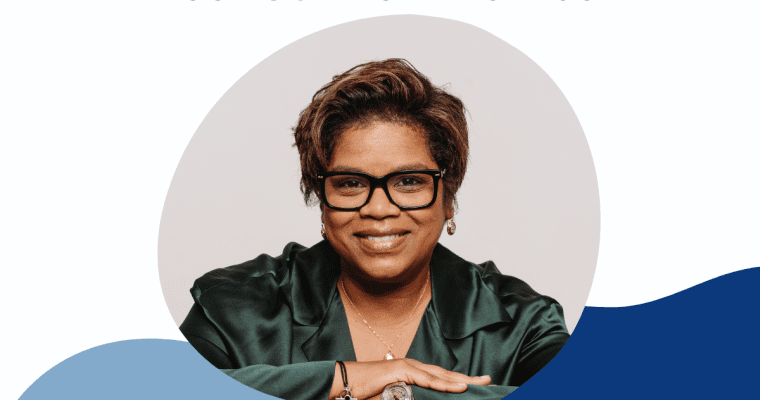
Please welcome our newest member from Canada, Tania Tanic
Tania Tanic is a senior executive in cybersecurity, artificial intelligence innovation, governance and digital transformation, with more than 27 years of experience in major Canadian and international organizations, particularly in financial services, public investment, technology and consulting. A CPA and certified corporate director, she holds …