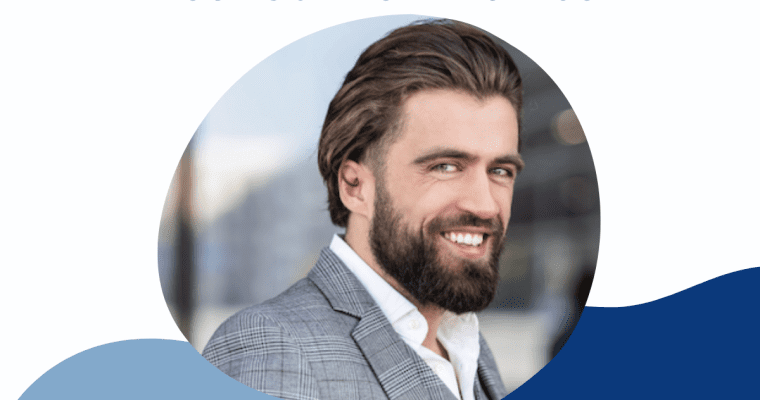
Please welcome our newest member from France, Régis Rocroy
Régis Rocroy is a self learning professional passionate about IT, cybersecurity, and now AI. With more than 25 years of experience in cybersecurity, he currently supports mid size companies as a CISO advisor and interim CISO, helping executive teams structure governance, align risk management with …